Documentation Rescue: Take Command of Your Security Infrastructure
You cannot protect what you cannot see. If your facility lacks accurate, up-to-date security blueprints, you aren't just managing a system—you’re managing a liability.
At CG Security Consulting, we specialize in Documentation Rescue. We step into complex, "blind" environments—older facilities, inherited campuses, and high-growth sites—to perform forensic digital mapping. We replace "guessing" with "precision," turning undocumented hardware into a strategic, data-rich asset.
The High Cost of Missing Documentation
Missing or "dirty" as-builts are more than just a nuisance for your facilities team; they are a threat to your operational readiness.
Proprietary Lock-in: Without your own drawings, you are tethered to a single integrator who holds your system’s "source code" hostage.
Inflated Maintenance Costs: Every service call becomes a "search and rescue" mission as technicians bill you hours just to find a junction box or trace a cable.
Strategic Blind Spots: You cannot perform an accurate Threat, Risk, and Vulnerability Assessment (TRVA) on a system that exists only in "tribal knowledge."
Our Recovery Intelligence: The Tech Stack
We don't use tape measures and clipboards. We use Reality Capture technology to build a "Digital Twin" of your security ecosystem from the ground up.
Mobile LiDAR Scanning: We use laser-point cloud technology to "paint" your facility, creating dimensionally accurate floor plans where none exist.
Aerial Photogrammetry (Drones): For large campuses and utility infrastructure, we deploy drone-based mapping to capture your entire perimeter in high-resolution, georeferenced detail.
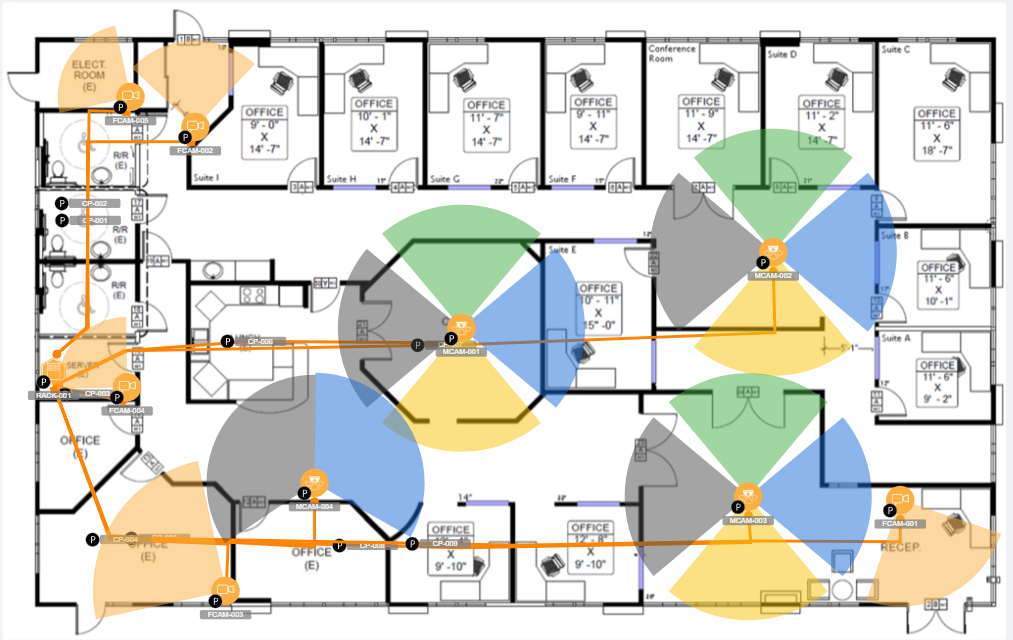
Security Design Integration: We overlay your physical assets onto these new digital canvases, creating a live, cloud-based "Golden Record" of every camera, sensor, and card reader on your site.
Your Deliverables: The "Golden Record"
When we "rescue" your documentation, we don't just hand you a PDF. We provide a comprehensive Security Intelligence Package that you own forever:
Digital As-Builts: High-resolution, multi-layered CAD (.DWG) and PDF files of your entire facility.
The Digital Asset Database: A cloud-based inventory including model numbers, installation dates, IP addresses, and warranty data.
Perimeter & Interior Coverage Maps: Clear visual proof of your "Line of Sight" and sensor detection zones.
The Maintenance Roadmap: A prioritized list of "Technical Debt" discovered during the mapping process.
From Chaos to Command
Whether you are preparing for a major system upgrade, navigating a NERC CIP compliance audit, or simply taking over a new facility, don't move forward in the dark.
CG Security Consulting provides the strategic oversight needed to turn your legacy infrastructure into a resilient, documented, and manageable ecosystem.
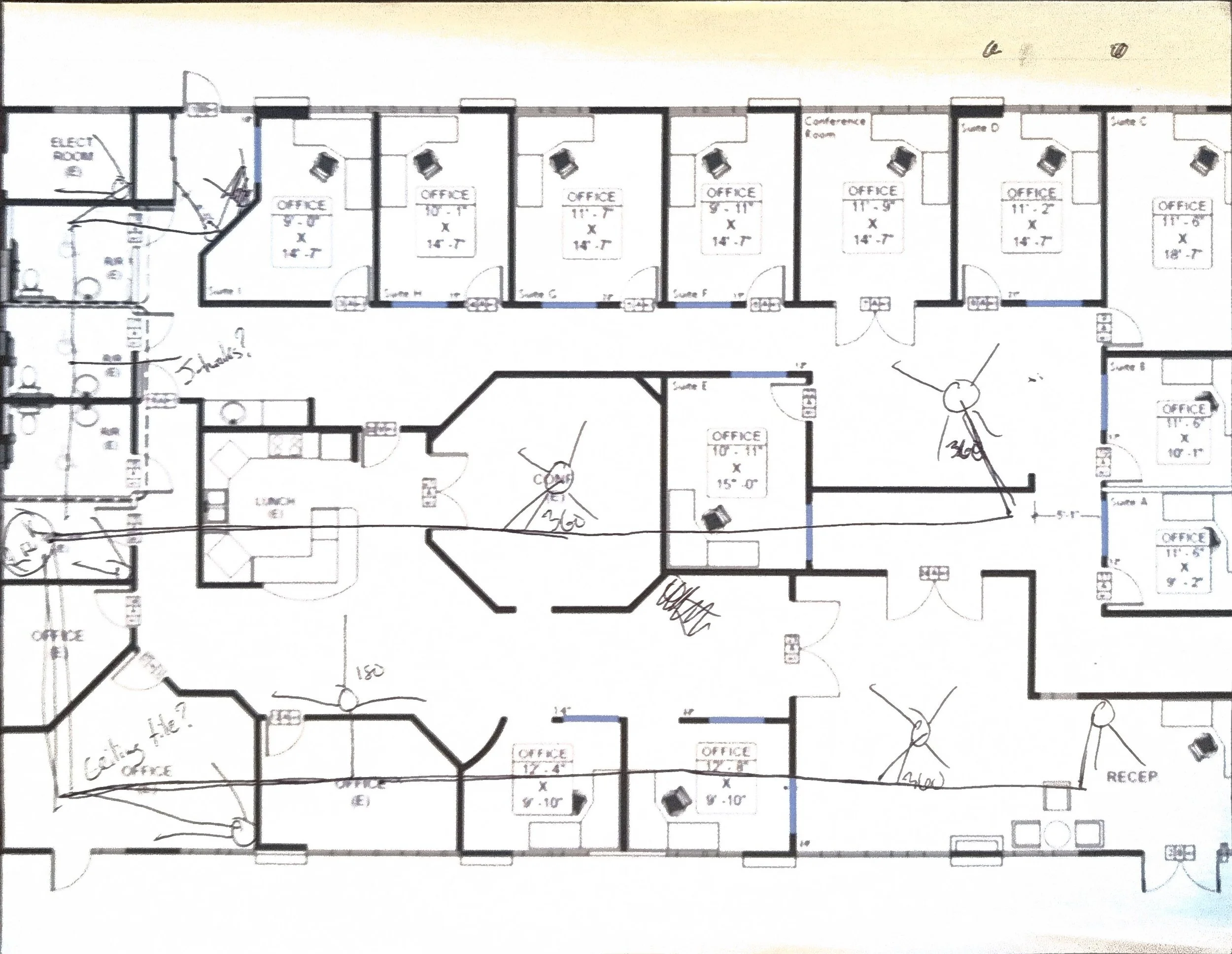
Hand-drawn Chaos
Digital Command
Ready to Rescue Your Documentation?
Stop paying for your integrator's mistakes. Schedule a consultation to digitize your facility today.